Today, we are releasing the next tutorial in our Apache / ModSecurity series:
Extending and Analyzing the Access Log
“What’s the big deal?” I hear you say. I admit, it may sound a bit boring, but log files are primordial. Configuring the right logfile makes the difference between ignorance and insight into you server. There are quite a few tutorials around that tell you how you can reconfigure Apache to write all sorts of funny information into the access log. But nobody tells you what information is actually important and what is bogus. Of course, it depends on your local setup, but in this tutorial, I present you a selection of fields which I find useful without logging everything and the kitchen sink. The format has evolved over the course of ten years and after two years without an update, it has matured in a way that makes it ready publication.
Key takeaways:
- We stick to the standard “combined” format and extend it to the right.
- The legacy and empty “logname” field next to the IP address has been replaced by the Country GeoIP code (strictly speaking, this is no longer combined format, but the format itself does not change)
- If you paid close attention in the 2nd tutorial, you saw that the Apache error log and the access log are configured to share the same timestamp format. This is a surprisingly new feature of Apache.
- The Unique ID of the request is being logged. This is the primary key that keeps various log files together.
- IO In and IO Out
- Deflate Ratio in percent
- SSL/TLS Protocol version
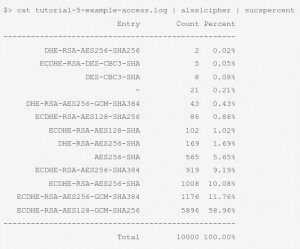
- SSL/TLS Cipher Suite
- ModSecurity Anomaly Scores
So that’s a good chunk of useful information. I am sure you can build great dashboards based on this. We will stick to the basics, though, and I will show you how to extract information on the fly with the help of a handy set of aliases like this:
Did I convince you? Here is the link to the tutorial again:
Extending and Analyzing the Access Log
The overview over all the published Apache Tutorials can be found here so you have the right foundation for this advanced tutorial. Follow me on twitter (@ChrFolini) to make sure you are informed when the next guide hits the shelf.
 Christian Folini Follow @ChrFolini Tweet
Christian Folini Follow @ChrFolini Tweet